Have you installed a browser extension only to later regret it? Many plugins can access your personal data before you even realize. Learn how to research add-ons to avoid malicious ones. Follow tips on assessing permissions, vulnerabilities, communications, and risk scores.
Security
Sadly, you can never be too safe online. There are just too many ways in which programs and people try to get at your data. However, there are various measures you can take. Some of these include educating yourself about certain bad behaviors as well as helpful services.
Be Vigilant Online: How to Avoid Falling for Suspicious URLs
This article delves into the common scenarios of encountering potentially harmful URLs. Learn to investigate sender behaviors, recognize red flags, and uncover the characteristics of suspicious URLs. Discover tips for checking short URL addresses and utilizing multiple tools to enhance your online security. Stay informed, ask questions, and be prepared for the unexpected while teaching your kids about the dangers of unknown links.
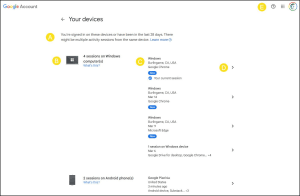
How to Find Devices Connected to Google Account
This tutorial shows how to see which devices have access to your Google account. Also includes details on checking for suspicious activity and removing items.
Stop Being Lazy and Get a Password Manager
Are you tired of remembering countless passwords? A password manager is your solution. It securely stores your passwords, generates strong ones, and fills them in for you. It’s more than just a password tool; it can handle license numbers, notes, and more. With minimal cost and maximum benefits, it’s time to stop being lazy and get a password manager.
Pair Authenticator Apps & 2FA Sites to Secure Your Accounts
Ever wondered about the safety of your online accounts? Learn about 2FA, a digital guardian for your data and authenticator apps. While hackers are becoming smarter, 2FA offers a reliable barrier. It’s not just about passwords anymore; it’s about having that extra layer of security. See how easy it is to set up.
Quick Guide to MAC Addresses & Filtering
MAC addresses: essential but often overlooked. Learn their format, how to find them, and how to use MAC filtering as a security measure. Want to selectively control network access and consider potential cloning issues? This article has the insights you need.
See Which Apps Access Your Google Account
We’re living in an interconnected world which offers a lot of conveniences. We can use Google, Facebook, OAuth to connect us to online services and apps. The downside is that there are more “bad actors” trying to trick us and gain access to our info.
Can Your Eyes Spot this Security Problem?
This is a time when people like to hunt for Easter eggs. Either the traditional ones or the clever ones that are hidden by software vendors. Both of these are fun. However, this one is more a rotten egg and it could cost us dearly if we don’t pay attention. And it all starts with punycodes and fake domains. The good news is there are several workarounds.
How to Handle Fake Security Warnings
Fake virus alerts that appear in your web browser appear to be on the rise. The objective of these alerts is to have you buy a service you don’t need. There are ways you can spot these annoyances and get rid of them.
The Surprising Impact of Browser Cookies on Your Web Journey
Ever wondered what browser cookies really are? They’re just small text files that store specific data, and they’re not as scary as you might think. The article breaks down their structure, covering seven key fields like name and domain. It also helps you tell the difference between first-party cookies, which are usually okay, and third-party cookies, which you might want to keep an eye on.
Password Protecting USB Drives
There aren’t too many things that upset me. One item that does is people who put personal data on their USB drives without password protection. They are just waiting for a disaster as sooner or later that thumb drive will vanish. The question is who will get the data next?