Ever had one of your online accounts hacked? It’s not fun. Learn to boost your account security with two-factor authentication (2FA) and authenticator apps. It’s a simple yet powerful layer of protection. It’s free and easy to set up and find 2FA sites.
What is Two Factor Authentication (2FA)?
The name two-factor authentication sounds complex to many users. Chances are you have already used it in some way but didn’t know it was called that. You might also hear it called “multi-factor authentication.”
Basically, it means that before you can access some service, you need to have 2 different things. These examples might include:
| Authentication Types | Examples |
| Something you know | account name, password, email account |
| Something in your possession | security key, application, code |
| Some physical attribute | fingerprint, facial recognition |
When you think of getting cash from your bank ATM, you’re using a similar process. You have to have both your ATM card and your PIN code. The online world can work similarly with a different set of verification codes and an authentication app or physical security key.
Instead of just relying on an account name and password, you can add a second protection level before people get access. This is important when you think of how many times you hear of security breaches from large companies or phishing attacks.
And sometimes breaches happen from our own actions. Maybe you logged into a friend’s computer and forgot to sign out. That’s why checking what devices are logged into our Google account is a good idea.

TextExpander: Worth It? Find Out.
Is TextExpander the right tool to boost your productivity? Get an independent assessment, weigh the pros and cons, and make an informed decision. Find out why I’m a fan.
Read the ReviewFind Popular 2FA Websites
You might be thinking that two-factor authentication is fine, but you don’t have any services that use it. You probably do, but many websites hide this security feature, and you have to go through extra layers to find it.
Here are some websites with 2FA you might know:
- Amazon
- Coinbase
- Apple
- eBay
- Epic Games
- Cloudflare
- Dropbox
- PayPal
- Evernote
- Xero
Most of the above companies are household names, but there are smaller players too. One good way to find 2FA sites is to go to https://2fa.directory/
Josh Davis, an Amazon engineer, started this 2FA directory site, but it is now maintained by a non-profit called The 2factorauth Group. The site offers ways to find sites that use two-factor authentication and additional information. The site is straightforward to use and presents the information in a nice grid.
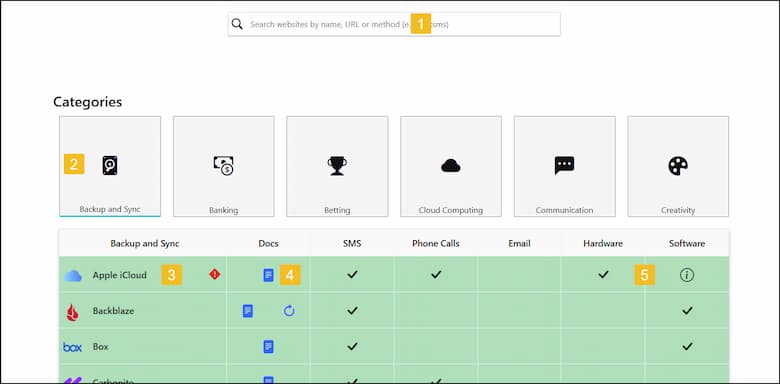
- There is a search bar at the top where you can enter a service name. As you start typing, the site will show possible matches.
- You can also filter by category. In my example, I’m using the Backup and Sync category.
- Any alerts or exceptions about the company or service.
- A link to that company’s two-step verification documentation.
- An indication of what authentication types the company uses. You’ll also note that you can send a tweet to the company asking them to support 2FA.
Start with an Authentication App
There are many methods you can use for two-factor authentication. Perhaps, the best-known service is Google Authenticator. Most sites that show a check in the Software column in the image above should work.
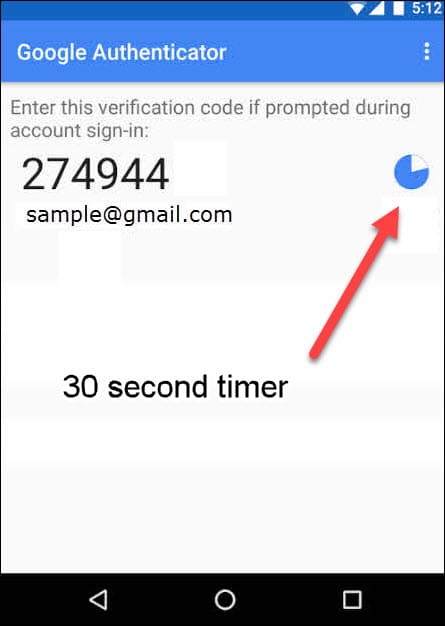
The way these apps work is to provide a one-time password (OTP) that you use to log in to a service in addition to your regular password.
For example, when I use Cloudflare, I sign in as normal with my account name and password. But right after I hit the Login button, I’m greeted with the dialog below since it’s a 2FA-enabled service.

At this point, I switch to my phone’s 2FA app and get authentication codes.
Using Google’s Authenticator
To use 2FA, you will need to install an authentication app on your mobile phone. In the case of Google, it’s available for both Android and Apple.
- Install the Google app from your appropriate store.
- Using the 2FA Directory, find your service instructions. Some websites have a separate security section where you may see the activation settings.
- Navigate to the service page and look for a QR Code. You will scan this code with your phone or tablet.

- Google Authenticator will add the service to your phone and provide a one-time password (OTP). In the picture below, my password was 274944. I need to enter this code into the confirmation box before it expires. The small circle represents how much of my 30 seconds are remaining. A new code is generated after that.
- Enter the code from your app into the service’s Confirm Auth Code box. Your service may use different terminology such as “second-factor token‘” etc.
- Your account is now configured to 2FA. You will be prompted to enter a new verification code from your app when you log into your service.
Other 2FA Application Services
There are several alternative apps in case you don’t like Google. They all work similarly in that they generate a time-based one-time password (TOTP) on a mobile device. These include:
For example, I prefer Authy and Microsoft Authenticator. While sites typically reference “Google Authenticator,” you can use your preferred app.
I suggest visiting each of these apps to see which one suits your needs. There are subtle differences, such as Authy doesn’t have a circle clock to indicate time but uses a bar at the top. And Microsoft’s version allows you to also store passwords. The app from Yubico also works with their hardware keys.
Caveats & Warnings
Although 2FA is more secure, it’s not bulletproof. This is especially true with SMS. While this is better than nothing, SMS is not secure despite banks still using it. I think the banks want you to use their own banking apps.
There have been some reports where these text messages were intercepted. Wired magazine had an informative article on this that you should read.
Another downside is that you may not be able to transfer your 2FA information when you get a new phone. The setup process doesn’t take a lot of time, but sometimes you need to take additional steps with the provider to remove the previous setup. Some programs let you scan the QR code from your old phone to the new phone and transfer information.
As much as I like 2FA, I have to admit some aspects can “bite you in the butt.” For example, I recently dropped my cell phone. The screen developed fine cracks starting in the lower-left corner and spreading upwards. I lost most functionality, including working with my 2FA app. The screen no longer responded to my taps. Fortunately, I had Authy on my iPad and was able to get around the issue.
I also realized some services I use had terrible fallback procedures. Most services will have a backup method so you can get into your account. The typical means include an SMS code or a stored list of backup codes that you enter into the app. However, some services tell you to call customer support. In one case, my domain registrar wanted a notarized letter.
I suggest double-checking your services before you do a factory reset on your cell phone or get a new one. Get a copy of the one-time codes you’ll need or set up SMS where possible.
These one-time codes are not the same as one-time passwords, although the concept is similar. These one-time codes are usually alphanumeric and stay active until you use them to log into your service. They don’t expire after 30 seconds. The codes can be used in cases where you don’t have your phone. The downside is you need to place them someplace safe that you can access. And no, printing them out and putting the list under your keyboard is not safe. But many password managers have note fields where you could store the codes.
If you have a provider that doesn’t have a fallback method, I’d suggest deactivating the service until you get the phone working. While it’s OK to keep hackers away, it’s exceedingly frustrating when you’re the one locked out. I might also be inclined to check to see what apps might have access to my Google account.
Although it takes time to set up 2FA with all your services, it’s worth the additional effort. You don’t have to add all of them at once. Start by adding the services that pose the greatest risk. Then, get used to the login process and add more accounts as you get comfortable.
