Have you ever downloaded a browser extension only to regret it later? I have. I failed to take the time to properly evaluate it. That’s why assessing any browser add-ons before installing them and periodically after that is critical. So, instead of relying on Google, Microsoft, and Mozilla browser stores, I now have a process to evaluate browser extensions.
Why You Need to Evaluate Browser Add-ons
I get it. You’re in a hurry and found a cool extension that can make some tasks remarkably easier. And some seem to make you more productive. However, here’s why you need to evaluate your browser extensions and add-ons before downloading and after.
- While people like Google, Bing, and Firefox try to catch bad actors, plenty of bad plugins get through.
- Sometimes an extension starts out legit but adds suspicious code at a later date.
- You won’t get a notification even if an extension is removed from a browser store.
- Malicious extensions can do things like change your search engine, inject ads, access your browser history, etc.
- Many malicious extensions can be very difficult to uninstall.
- These extensions may ask for permissions they don’t need.
- They may conflict with other software or use system resources.
Update: Starting with Chrome 117, Google will flag malicious Chrome extensions that have been removed from the store.
One benefit of writing this article is it made me question if I needed all the plugins I’d already downloaded. And how often did I use them? My rule of thumb is the fewer you have, the better.
I also don’t download extensions that aren’t in a browser store. Ask yourself why isn’t this extension in Google, Bing, or Firefox’s repository.
Human Factor vs. Automated Tools
Early on, I would do the “eyeball security method.” That pretty much meant my reading about the plugin and whatever reviews showed. You can glean a fair amount of information. For example, if I’m looking at the Momentum extension, I can gather the following information:

- The extension has a “Featured” badge, meaning it underwent a human review.
- It has over 3 million users.
- It has a substantial number of users and a high overall score.
- There is a website associated with the extension.
If I scan down the page, I get additional information.
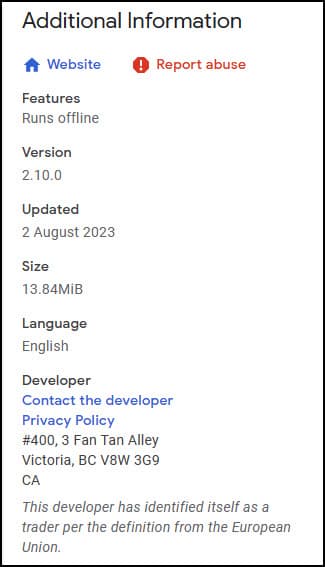
A key point for me is whether the extension was recently updated. My preference is for products that are actively worked on.
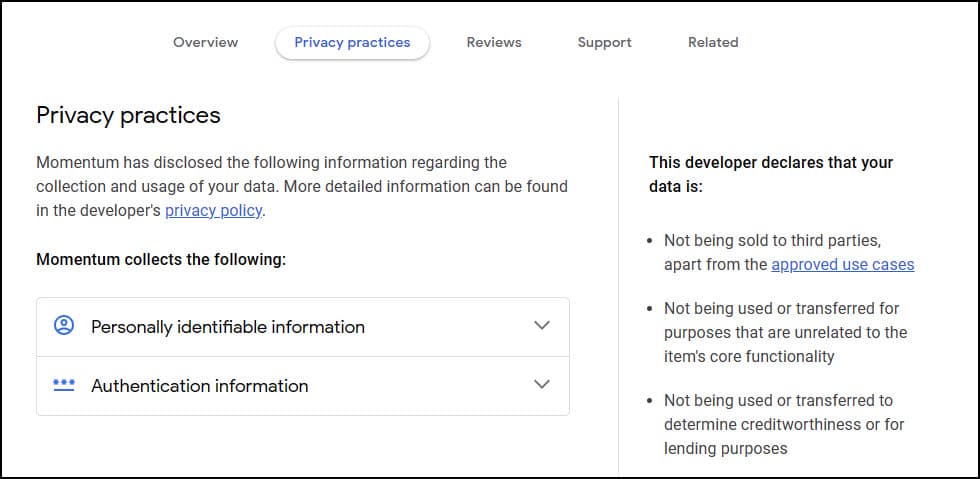
And if I click the Privacy practices link, I get a good idea of how they handle my data. And since I did a Momentum review, I know you need to create an account and possibly supply financial information if you want to use all the features.
Another of my eyeball tactics is to look at the User Reviews. I’m not going to read all of them. I do concentrate on the most recent ones. These reviews can be helpful if the extension has been recently sold or the focus has changed. But you must also realize Google, Bing, or Firefox don’t verify reviews.
At this stage, I have a good gut feeling. However, using risk analysis tools to gather additional data is prudent. This can be very useful for evaluating an item you’ve already installed.
What is CRXcavator?
CRXcavator is a free service created by a division of CISCO called DUO Security. It started as an internal tool in 2019 and still carries a beta label. You may remember DUO Security, as I mentioned their mobile authenticator app in our article on using 2FA to protect your online accounts. The service evaluates browser extensions based on criteria and provides a risk score you can track over time. You can use the service with plugins that work on Chrome, Firefox, or Edge.
Although the tool was designed for internal use, we can benefit. I won’t cover all sections here as some are quite technical. There is an option to create an account, but that is for people who manage corporate networks. I didn’t create one.
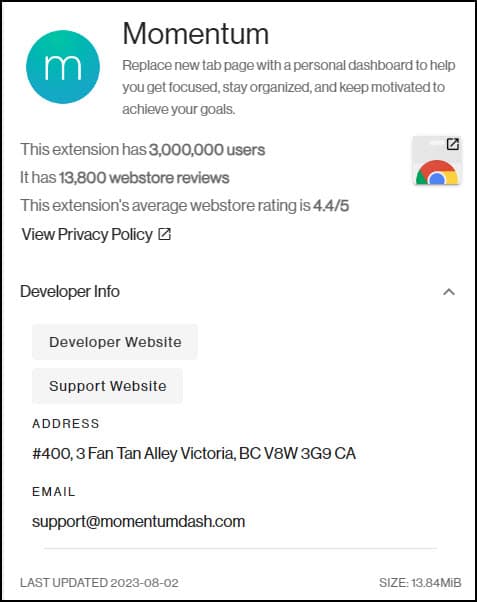
Once you’ve supplied the plug-in name or URL, you’ll get a report divided into two sections. The left section provides basic information such as:
- Extension name and a brief description
- Webstore rating
- Privacy policy link
- Developer website
- Developer email
- Last updated
- Version
- Source Code
The right section focuses more on risk. It includes:
- Risk Scores in 6 categories
- Risk Over Time
- Permissions
- Content Security Policy
- External Communication
- RetireJS Vulnerability Scan
- Requested OAuth2 Scopes
- Related plugins
While you may not use all this data, I’ve found it useful when comparing plugins that do similar functions.
Finding Your Browser Extension or Add-ons
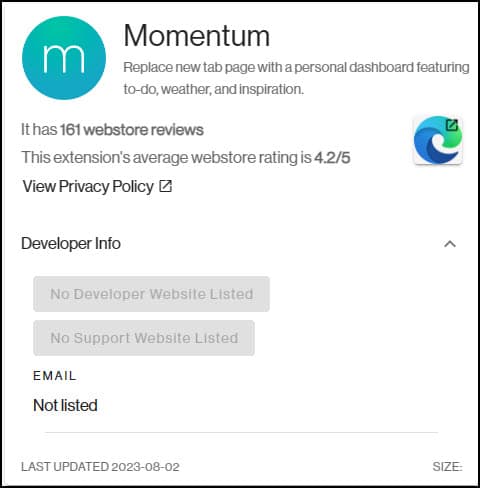
According to the documentation, CRXcavator regularly scans the various browser repositories. This means that if your extension is in a browser store, the service will most likely have an evaluation. Although the Microsft Edge browser can use Chrome Extensions, I prefer to use Chrome for these purposes. I’ve seen examples where more data shows, such as Developer Contact info, size, and review counts.
- In your browser, navigate to https://crxcavator.io/
- Click the down control to the right of All and select your browser.
- Start typing the extension name in the Find or Submit an Extension textbox.
- Click your extension name. In my case, I’ll use Momentum.

Here’s an example where the service shows more info for the Chrome Version
Although the Developer Info is in the Edge Add-Ons store, it doesn’t get picked up by CRXcavator. It may be an issue with how the data is stored.
Assessing Plug-in Risk
You won’t see anything about the user interface or effectiveness. The tool’s focus is on security vulnerabilities. However, it provides meaningful clues that can help you determine if you want to use the browser plugin or add-on. The first item I look at is the Total Risk Score. This is beneficial if you’re debating between several plugins that do the same thing.

In the case of one coupon extension, I saw a score of 802. The higher the score, the higher the risk. I’ve seen ranges from 144 to 2093. After using the tool for a while, you might see some patterns. For most extensions, the biggest part of the score tends to be allocated to the Content Security Policy. However, in the example above, the extension had additional Permission issues and JavaScript vulnerabilities.
Browser Permissions
The Permissions section will classify items based on risk. I look out for the ones classified as Critical and High. That doesn’t mean I automatically reject items with these classifications. Some extensions need these permissions to function properly. In the case of HTTPS Everywhere, you may see the plugin flagged for “Gives your extension access to the chrome.webRequest API” or “Gives your extension access to run on all sites and schemes”. In this case, the extension ensures the user goes to the secure web page version, which is the desired behavior.
In contrast, I might hesitate on a coupon code extension. While they may grab your checkout URL to look for coupon codes, they may do other things, such as monitoring your purchase.
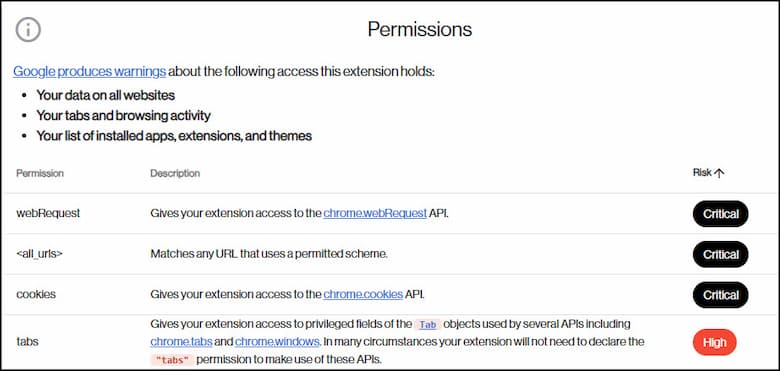
This is also a good opportunity to find any listed support email address and ask them why the extension needs certain permissions. If you don’t get a reply, I’d cross them off your list.
I’ve also used the tool in combination with ChatGPT and Claude. Some of the provided links go to developer web pages and are technical. I’ll copy a passage of text and ask the AI tool to explain it to me in simpler terms.
How is Risk Over Time
We all make mistakes, and that includes developers. You want to watch out for extensions that show the wrong trend. Ideally, you want to see the Risk Score trending down. You can hover over the trendline to see a certain date’s version, date, and risk score.

Are There Known JavaScript Library Issues
The highest risk score I’ve seen was over 2000. Of that amount, 1650 of the score was due to JavaScript vulnerabilities. It had 14 rows worth. This made sense because the plugin hadn’t been updated in 4 years. It’s probably been abandoned by the developer. But that doesn’t help people who use it.
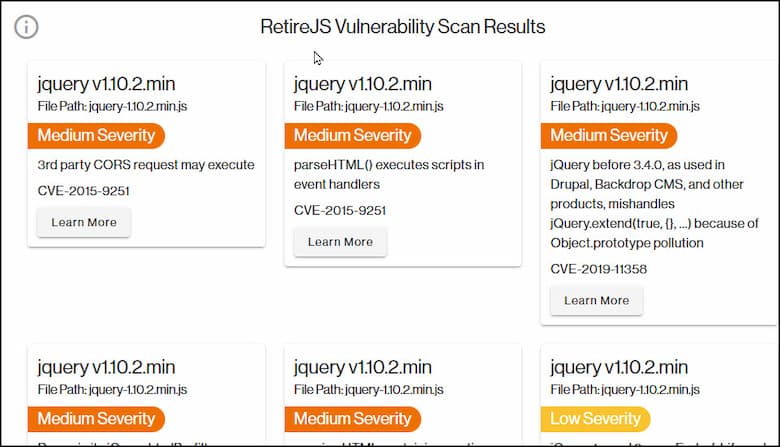
Clicking the Learn More button on one of these items opens a pop-up where you can see the GitHub Advisory Database with more detailed information.
External Communications Calls
Many extensions do make calls to external sources for legitimate reasons. For example, they may have links to their social media accounts, plugin documentation, Wikipedia, Google Fonts, and so on. Remember the add-on’s purpose and think if it makes sense for these calls.
The main thing to look for is any domains that look odd. This isn’t always easy to tell, and I wouldn’t copy the link and open it in your browser unless you were using some sandbox. Instead, I would suggest some of the resources I mentioned in my article on checking suspicious URLs.
Key Points & Takeaways
This article shows some easy steps you can take to protect yourself from bad extensions. For people who are technical, you can dive deeper with these tools by reviewing the source code.
- Evaluate a browser extension before downloading to avoid malicious extensions.
- Be careful of brand-new extensions regardless of the review count.
- Browser extension stores like Google and Mozilla can miss catching bad plugins – don’t fully rely on them.
- Check if the extension is actively maintained and updated.
- Use AI tools such as ChatGPT or Claude to explain terms you don’t understand.
- Use automated tools like CRXcavator to analyze permissions, vulnerabilities, communications and other risks.
- Watch for high-risk permissions that don’t align with the plugin’s purpose. Ask the developer to justify them.
- Look for odd external communications that don’t fit the purpose. Use URL-checking tools if needed.
- Routinely check your existing add-ons for vulnerabilities.
