We all have a variety of apps and services that we sign in using Google. These Google-connected apps range from email to maps and even Alexa. But what if you no longer want these apps to access your Google Account? This tutorial will help you know which apps are accessing your account so that you can turn them off.
Apps vs. Devices
There are many ways to access your Google account. This includes both software and hardware. This tutorial deals with software or apps. I did a separate tutorial on how to see which hardware or devices access your Google account. Ideally, you should check both.
Why Grant Google Access
You’ve probably noticed that you can log in with your Google account when signing up for online services. This often makes it easier, so you don’t have to remember another password. It could also be the service that needs to access some Google service or components like your contacts, Google Analytics, Google Calendar, etc. It’s become so familiar that we seldom pause when granting access.
Apps with Access to Your Account
Apart from approved applications, some “bad actors” like to devise ways to gain access. These attempts can come in many forms, so checking which apps have access is a good practice. A recent phishing attack made me review whom I granted access to, including third-party apps. It was enlightening as there were online services that I’d stopped using. And some that I couldn’t remember. It allowed me to do a security checkup.
How to Check Google Account Access
I should mention that Google has several security tools. This “apps with access” page is part of a larger umbrella that you can find at https://myaccount.google.com/security.
- In your browser, go to https://myaccount.google.com/permissions
- You’ll see a list of current services (1) you’ve allowed and their permissions (2). In my example below, you’ll see they’re not all Google apps. I have an Amazon Echo (3), which can access certain features. I can say, “Alexa, what’s my next appointment?” and she reads my Google Calendar.

- If you see an item you don’t need or recognize, you can click it to get more details. The panel will expand with more information, including the app’s name (1), access rights (2), and date you approved access (3).

- In this case, I know the Optimizely app, but I no longer need the functionality so I can click the REMOVE button to revoke access.

TextExpander: Worth It? Find Out.
Is TextExpander the right tool to boost your productivity? Get an independent assessment, weigh the pros and cons, and make an informed decision. Find out why I’m a fan.
Read the ReviewLevels of Access
As you can see above, there are multiple access levels. Some access is minimal, whereas other apps have “full access.” Full access isn’t entirely correct as these apps can’t change your pop-up settings or change browser notifications. You need to be careful and trust the apps that have this level of access.
Another item to review is whether an app has “read and write access.” Many legitimate apps do. For example, you may have a phone app that automatically updates Facebook with how many miles you ran or your sleep.
My rule of thumb is if you don’t know the app, remove it. If revoking access breaks something, the app will let you know it needs to be reauthorized.
What is this App or Service?
The biggest issue I’ve encountered is not recognizing an app or service. For example, I spotted this one – Project Default Service Account.
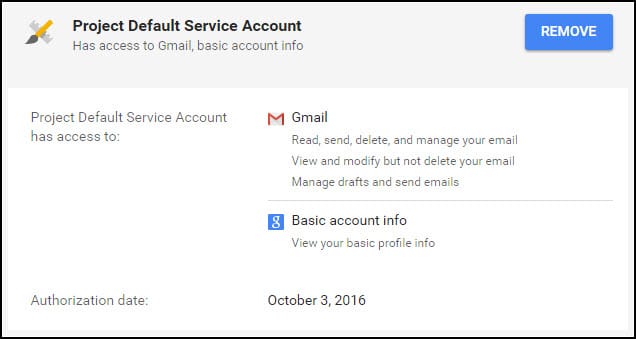
I haven’t a clue what it is, even considering the Authorization date. If I Google “Project Default Service Account,” I see several suggestions.
- A developer who used a default name when generating an application using the Android SDK.
- Bitdefender
- SyncMe
In this case, I’ll remove the authorization and see if some app stops functioning. Better safe than sorry.
Another example I’ve seen reports for was for project-xxxxxxxxxxxx and the x’s represent numbers. This makes it more difficult to search. Even if you search “what is project-xxxxxxx?” you’ll probably not find much since the number string appears to be unique. It looks like these might belong to various phone apps that reward people for playing games.
This tutorial just focused on Google Account security. Now might be the time to look at other services you use, such as Facebook, to see if the same problems exist.
