Ever opened an email that’s supposedly from a familiar source, yet something about it doesn’t look right? You’re not alone. This is a common scenario that could indicate the presence of a potentially harmful URL. I recently found myself in such a situation and started researching some suspicious URLs.
If the email hadn’t come from a friend, I would’ve deleted it. However, I was concerned that an email account might have been compromised. This wasn’t out of the question, given the number of security breaches. Moreover, with the explosion of various AI services, it’s easier for people to construct more sophisticated phishing attacks.
There are several ways to investigate emails and suspicious URLs, but here’s my process based on what I could see. As a policy, I don’t open these types of emails. Instead, I’ll either do the research or email my friend back, asking them if they sent it.
Know the Sender’s Behavior
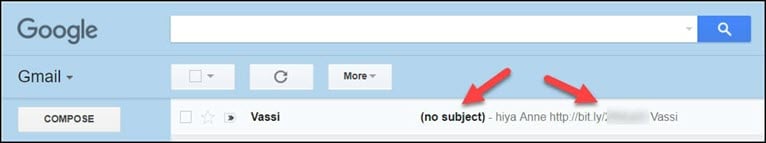
At this point, I see my friend’s name but not his full name. Many email applications, like Gmail, show the full email address when you hover over it with your mouse (1). So when I hovered, I could verify it wasn’t his email. Another clue is my friend doesn’t have his picture/avatar shown as usual. Instead, this email used the generic blue icon (2). A third clue is the sender didn’t provide a subject. Instead, it shows as (no subject) (3).

While it’s possible my friend would forget a subject line, the other items require him to change his email account settings.
Another example happened this morning. I got an email saying my Instacart account had been locked due to excessive login attempts. Since I use a password manager, I knew I wasn’t the one who locked the account. Doing a quick mouse-over on the sender showed the correct domain.
The email requested I click a link to reset my password. The greeting was off, and there was no branding. I pulled up a real email from the company and compared them. There were obvious differences, but gone are the days when we could pick off these emails by spelling and grammar mistakes.
Even if the logos showed, I never click those links. I go to the website directly if I suspect I was locked out of any service. I don’t use an email-provided link. This is another good reason to use two-factor authentication (2FA) when possible.
What Makes a URL Suspicious?
My first take is any URL that I don’t recognize, primarily the domain, needs further investigation. However, here are some other guidelines.
- Is the domain name spelled correctly? This is especially important if it looks like a business or service you know. The brain is really good about filling in missing characters. Some people call this typoglycemia. Look for extra letters, missing letters or substitutions. ( Example, 0’s for O or 1’s for l’s.)
- Does the domain name have extra words you haven’t seen? (Example: amazon-bestbuy.com)
- Is the business using a different TLD than you expect? The TLD stands for top-level domain and are the letters that follow the period. For example, on timeatlas.com, the TLD is “.com.” Some bad actors will buy other TLDs. (Example: .biz, .info, .xyz)
- Is the domain using subdomains? A subdomain appears before the domain, such as tutorials.timeatlas.com. On the surface, subdomains are harmless. But what if I used Amazon or Paypal instead?
- Does the domain name contain special characters or punycodes? Punycodes are a way to translate foreign letters to ASCII. Hopefully, all modern web browsers have fixed the security issue that Xudong Zheng referenced. Hmmm..it looks like Apple, but is it?

Are Short URLs Dangerous?
For the most part, these are OK. The problem isn’t with the service but with the creator’s intent. If you’re unfamiliar with URL shorteners, they are services that can take a long URL and provide a shorter one. The reader can click or type the short link and be redirected to the longer one. These can be very convenient.
Several companies provide this service, such as Bit.ly. Some companies also buy short domain names to shorten their URL. For example, Amazon uses amzn.to for their affiliates so users don’t see long URLs.
For example, if I wanted to create a short URL for my TextExpander review, I would enter the regular web address in the Destination field.

I get the new web address after I hit ENTER at the top. In my case, the regular URL is shortened to bit.ly/text-expand.
How to Check Short URL Address
While these URLs solve one problem, another arises. What’s the final destination? You can’t hover over a short link with your mouse to see the full URL. You’re running blind. Fortunately, some URL scanners will expand the shortened URLs to the full version. In my testing, the services that offered web application firewalls (WAF) fared best. This is because they did a deeper inspection.
Cloudflare Radar URL Scanner
This free service is in beta but does an excellent job as it provides additional domain info. While scanning takes longer, it also shows the additional UTM parameters. If you’re wondering about UTM parameters, they are optional items appearing after the question mark. They are mostly used for analytics. In my case, I’m curious if people click short links.
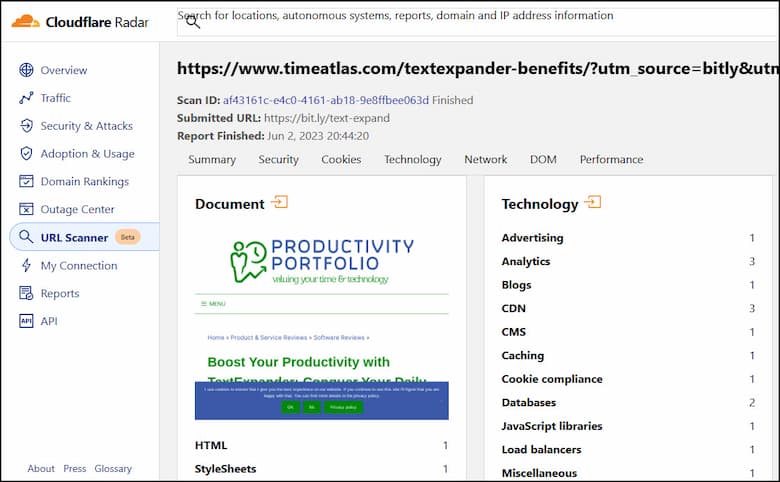
What I appreciate about Cloudflare is they also provide an image of the page. And if you look toward the top, you can see the URL I submitted.
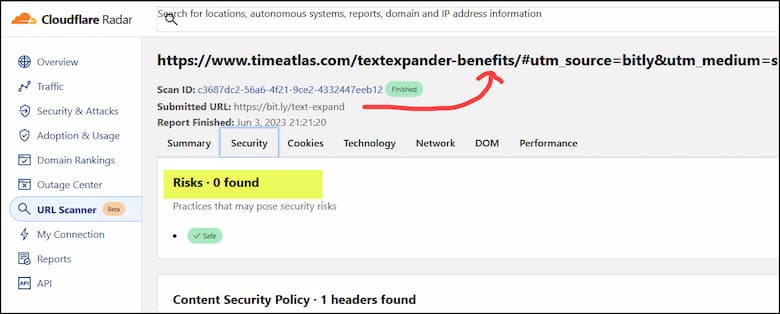
If I click any of the top headings, I see more details. For example, clicking the Security heading provides a view that highlights Risks. I can see my Bit.ly URL didn’t trigger any risks.
SUCURI Site Check
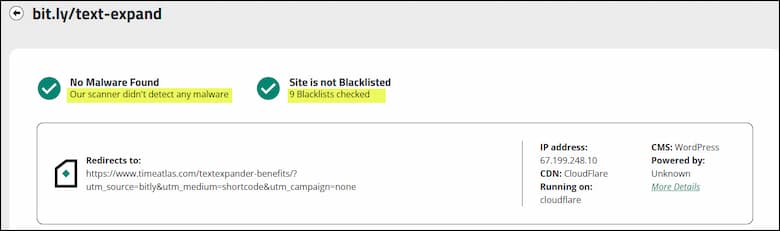
SUCURI is a popular WordPress security service that also offers firewall protection. Most people probably use this service to see if their site has been hacked. However, it can show details on short links. In addition to showing the URL I’ll be directed to, they check for malware and do a blacklist check on the domain using the following:
- Google Safe Browsing
- McAfee
- Sucuri Labs
- ESET
- PhishTank
- Yandex
- Opera
Use Multiple Tools
When researching possible malicious URLs, it helps to use additional resources. Each one supplies its analysis technology. For example, some services focus on domains, while others get down to a specific page or file. Moreover, some services scan the URL, while others consult a database or the community. And sometimes, they can provide conflicting info.
For example, one of my favorite security tools is VirusTotal. Unlike other services, you can research suspicious links or upload files. However, the automatic scans seem to have one vendor who flags Bit.ly as a malicious URL. This also happens if I use the root domain, not my TextExpander link.

Look Alike URLs and TLD
Above, I referenced misspellings and punycodes. But now we have to worry about new TLDs known as file extensions. For example, we can now buy domains ending in .zip and .mov. Most people equate these with a zipped file (.zip) or a video format developed by Apple (.mov).
The problem with these new TLDs was nicely highlighted in a Medium post titled “The Dangers of Google’s .zip TLD” by Bobbyr. His detailed article asks if you can spot the evil link. Take your time, as there are some visual clues.

I won’t spoil his question by providing the answer; I think people should read the article. It will help you see how people can disguise URLs and trick users into downloading dangerous content or sharing personal information. These are tactics legitimate websites wouldn’t use.
Two quick tips after reading this article are:
- Hover over the URL or anchor text to see what shows in your browser’s status bar.
- Right-click the URL or anchor text and copy and paste the link into an editor like VS Code or Windows Notepad.
Researching Domains
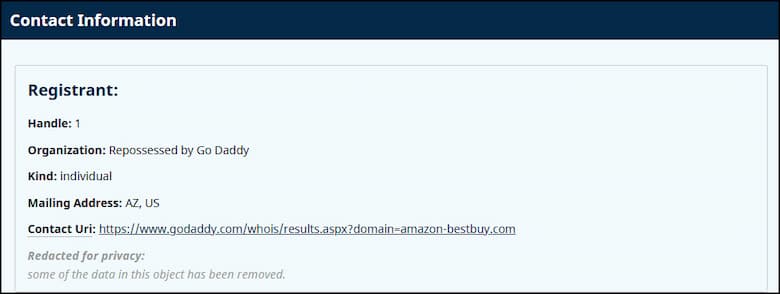
When updating this article, I put in a placeholder domain called amazon-bestbuy.com. On the surface, it’s a name that would make me pause, but I also wanted to see if it existed without entering it in my browser’s address bar. This is where WHOIS lookup services can provide helpful information.
I’ve been using this service for years. While there are plenty of WHOIS lookup services, this one offers more information even if you use the free service. For example, it tries to provide a thumbnail of the homepage and various statistics about domain changes. If you scroll down to the Whois Record, you can see additional info.
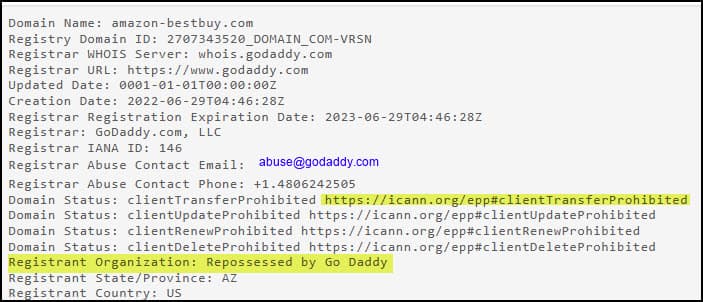
This is an example of a domain taken out of circulation. Perhaps, Amazon or Bestbuy contacted the domain registrar. Or the site violated the registrar’s terms of service.
I can also go to the ICANN lookup database and see a shorter version.
These services can provide additional clues. Remember when I mentioned knowing the email sender’s behavior? Well, the same is true for domain owners. Going back to my bogus Instacart email, the phishers bought a domain with a similar name. But there were numerous differences if you compared the registration with the real Instacart.com. My experience is when companies have multiple domains, they use the same registrar, contact info, and nameservers. It makes it easier to maintain.
Final Thoughts
The bottom line is staying safe online is getting harder. New technologies, like AI, are changing the game. Hopefully, in the future, AI tools will make malicious URLs extinct. Till then, the tools referenced above can help. But don’t forget: no system is perfect. Remember, it’s up to us to protect ourselves online. Stay informed, ask questions, and always be ready for the unexpected.
If you have kids, start teaching them now about the dangers of clicking unknown links or researching browser extensions before installing them. Another good resource is ConnectSafely.
